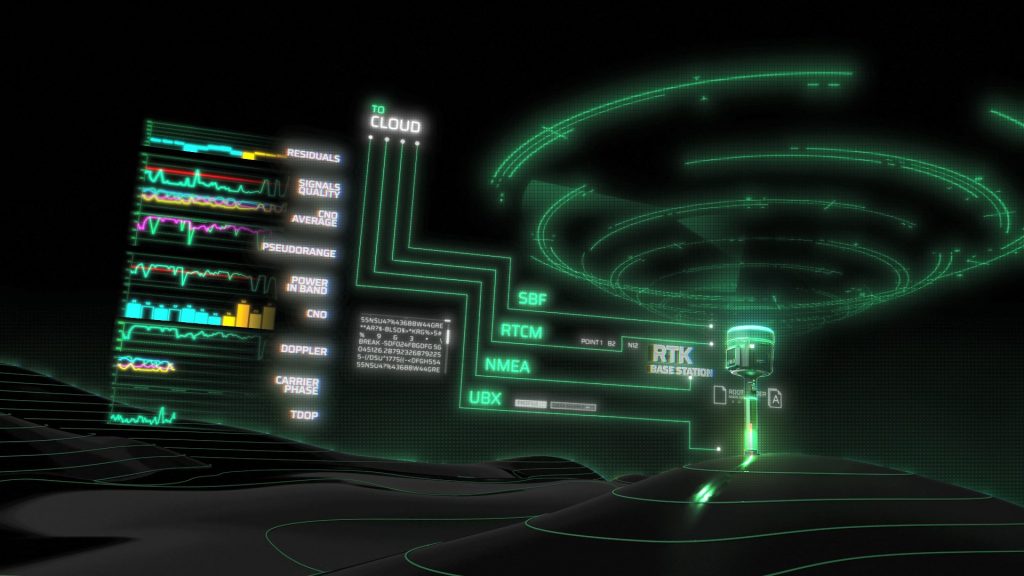
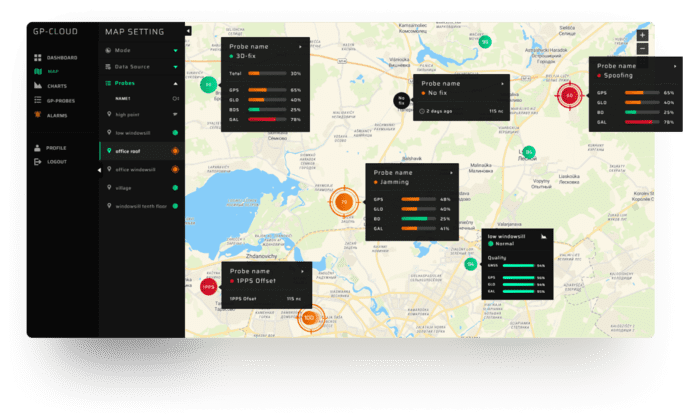
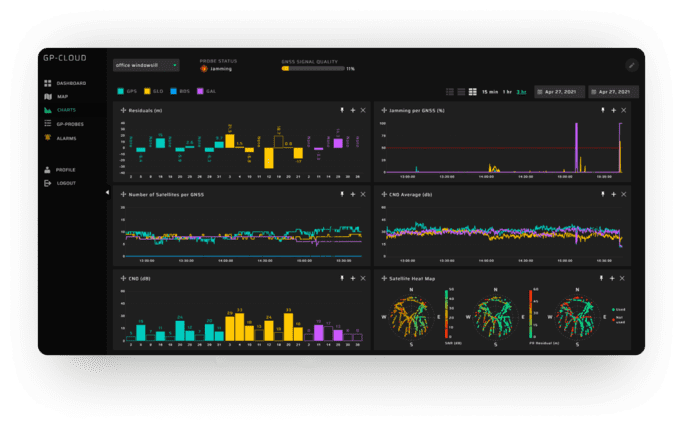
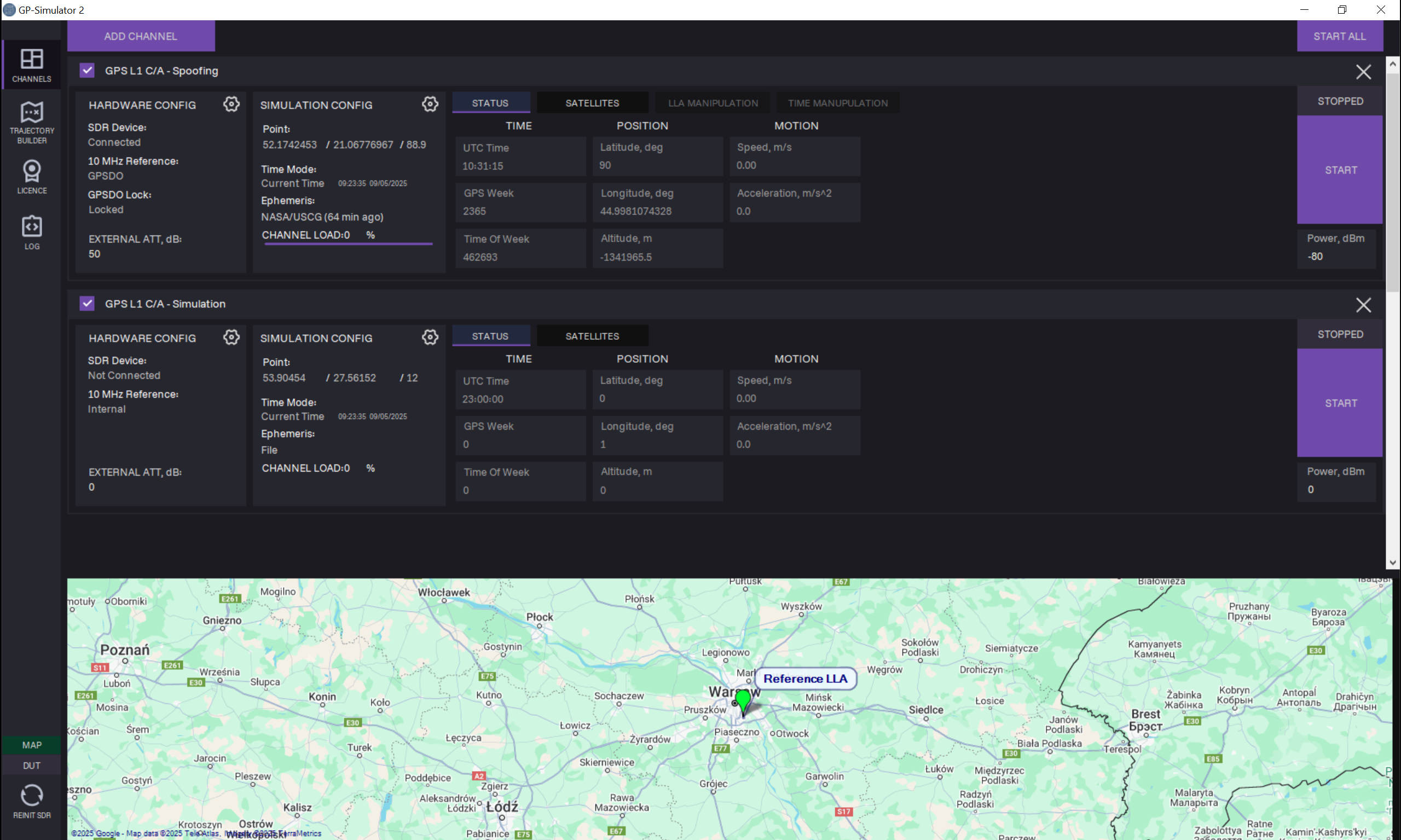
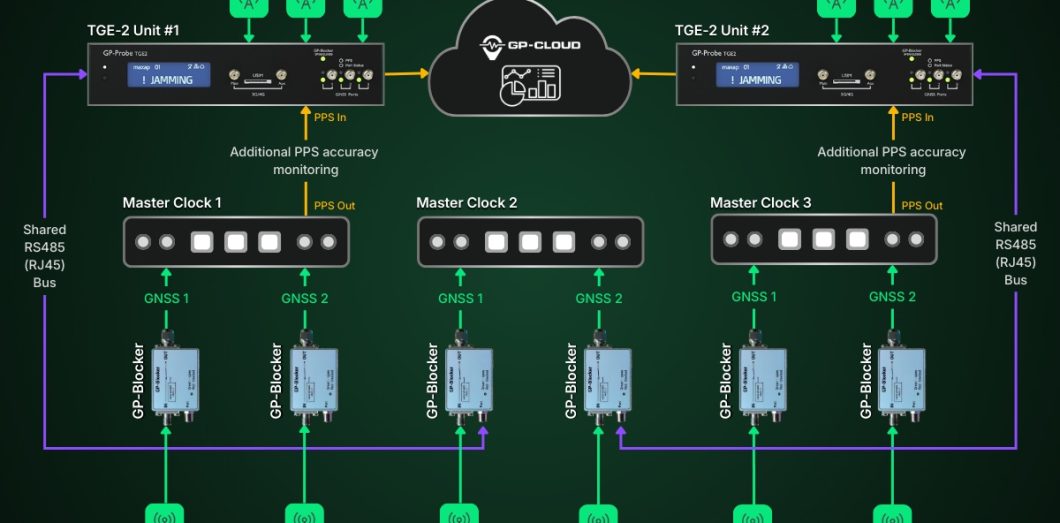
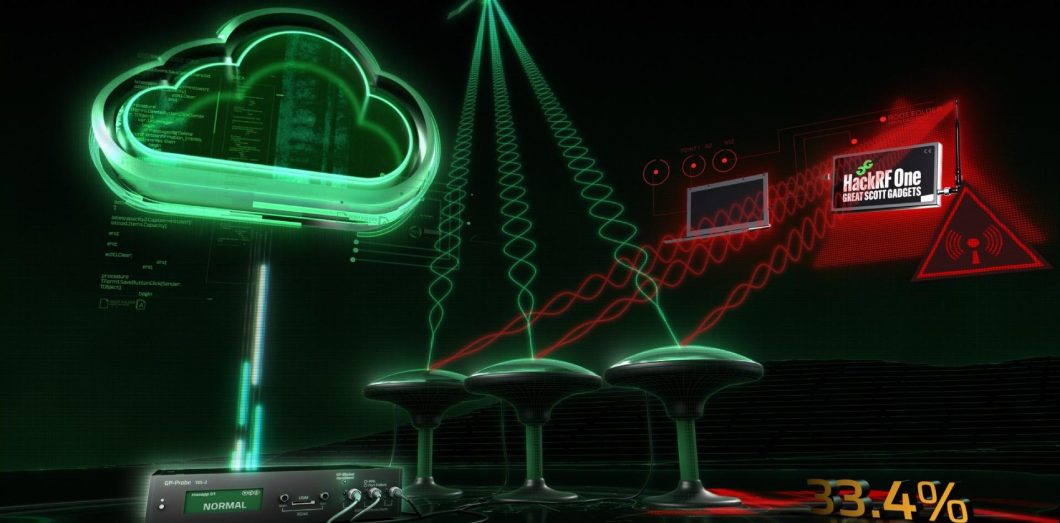
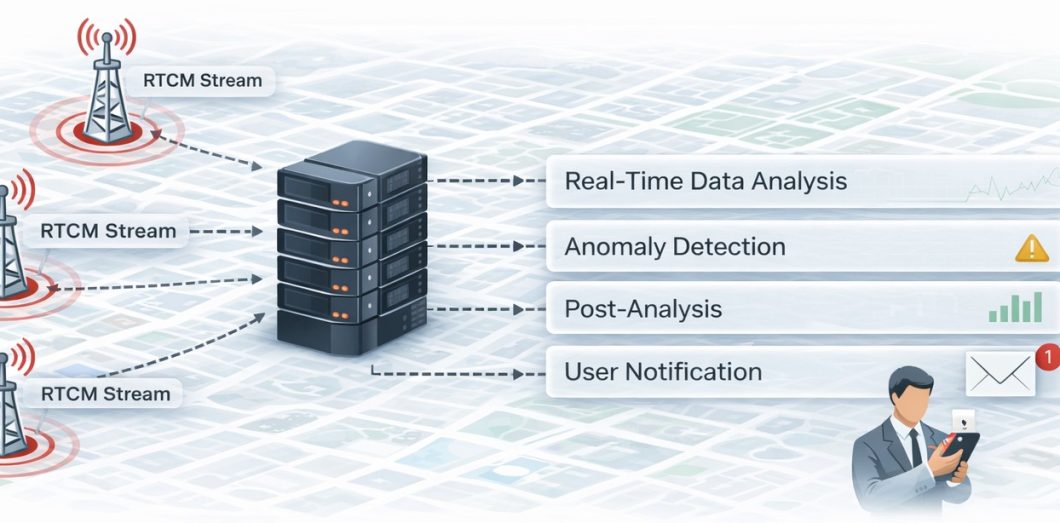
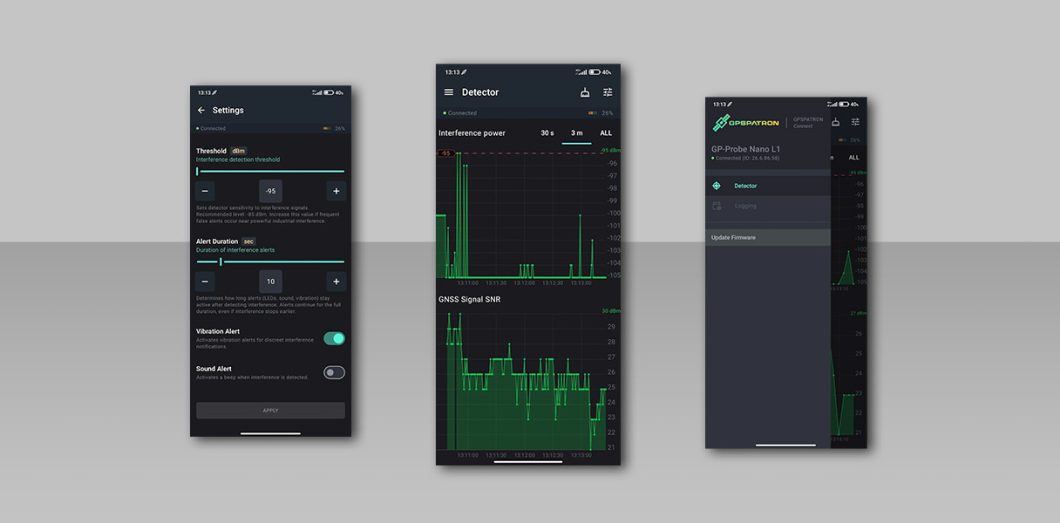
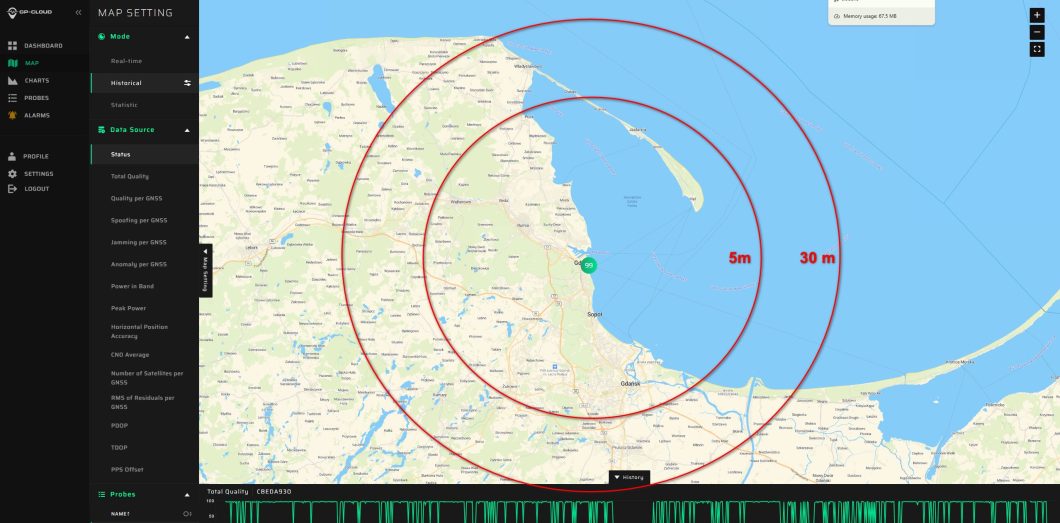
We provide the most robust GNSS cybersecurity solution on the market. In combination with a three-channel GP-Probe, the solution can detect sophisticated GNSS spoofing attacks in real-time.
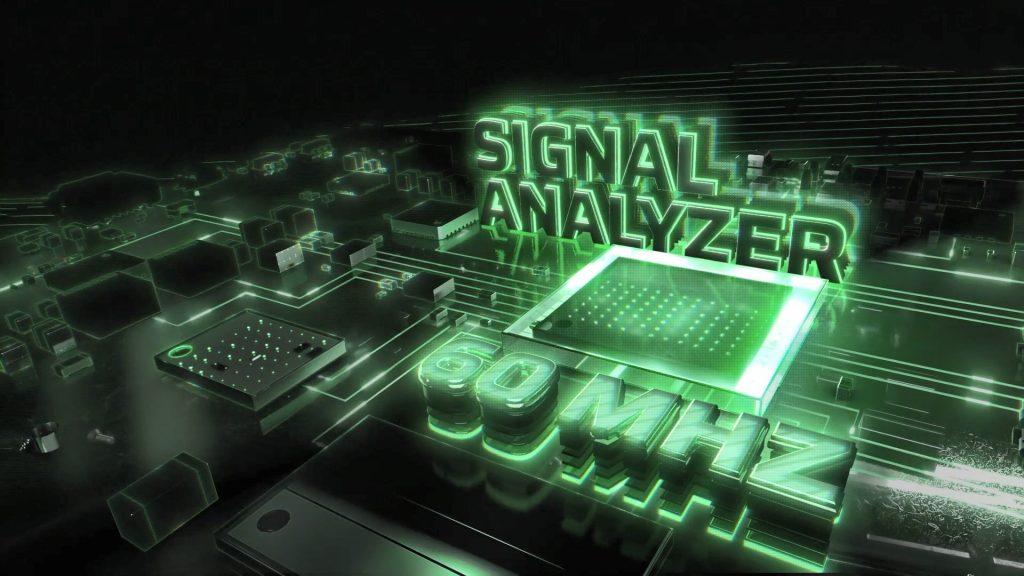
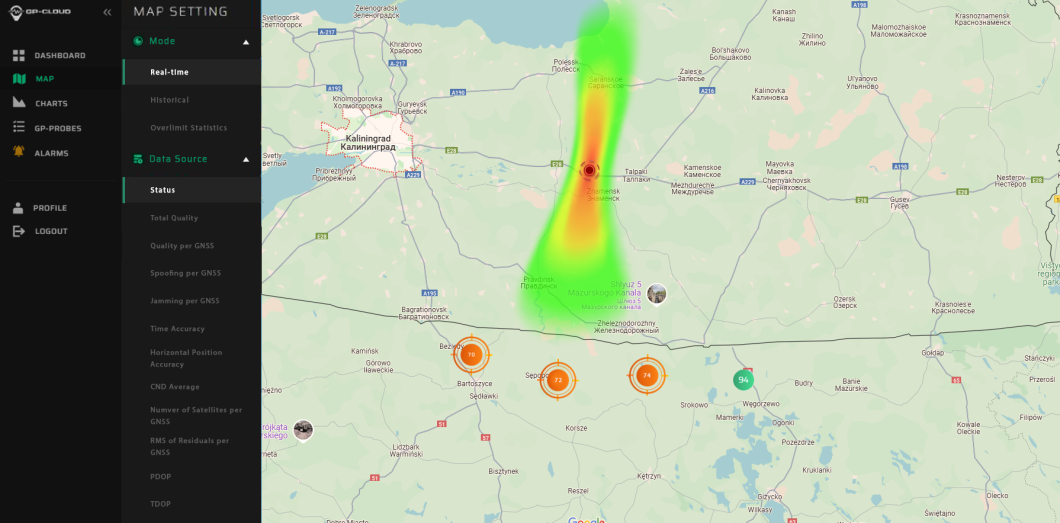
Check out the exceptional performance of our system in JammerTest2023!